Oh my Satoshi
2011-09
Bitcoin P2P Currency: The Most Dangerous Project We've Ever Seen
May 15, 2011
by Jason Calacanis
Solid discussions of this piece on BoingBoing.net, Hacker News, Slashdot and Reddit. Rob Tercek has a follow up to this piece here.
by Jason Calacanis and the LAUNCH team
A month ago I heard folks talking online about a virtual currency called bitcoin that is untraceable and un-hackable. Folks were using it to buy and sell drugs online, support content they liked and worst of all -- gasp! -- play poker.
Bitcoin is a P2P currency that could topple governments, destabilize economies and create uncontrollable global bazaars for contraband.
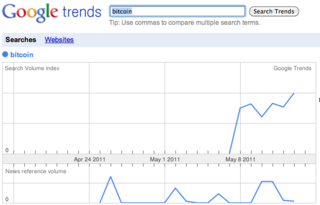
I sent the 30 or so producers of my show This Week in Startups out to research the top players, and we did a show on Bitcoin on May 10. Since that time the number of bitcoin stories has surged.
After month of research and discovery, we’ve learned the following:
1. Bitcoin is a technologically sound project.
2. Bitcoin is unstoppable without end-user prosecution.
3. Bitcoin is the most dangerous open-source project ever created.
4. Bitcoin may be the most dangerous technological project since the internet itself.
5. Bitcoin is a political statement by technotarians (technological libertarians).*
6. Bitcoins will change the world unless governments ban them with harsh penalties.
[...]
Bottom line: The world is going to be turned over by bitcoins unless governments step in and ban them by prosecuting individuals.
This is about to get really interesting, everyone.
Full article on original source:
http://www.launch.co/blog/l019-bitcoin-p2p...
"The root problem with conventional currency is all the trust that's required to make it work. The central bank must be trusted not to debase the currency, but the history of fiat currencies is full of breaches of that trust. Banks must be trusted to hold our money and transfer it electronically, but they lend it out in waves of credit bubbles with barely a fraction in reserve. We have to trust them with our privacy, trust them not to let identity thieves drain our accounts."
— Satoshi Nakamoto


SUNDAY, 23 OCTOBER 2011
The coming future
Right now, disk storage doubles each year in capacity. CPU power doubles each 18 months. Fibre speeds and capacity double each 9 months.
This is exponential growth in a wide scale. This is the type of technological change that economists call disruptive change. There is not a visionary on Earth who can forecast what this will truly mean in 20 years. Even 10 years is astounding. Just take some of the figures that this leads to by 2020:
Hard disk drives (likely memory based and at phenomenal speeds and with low power sleep states that provide an instant start capacity). Two (2) Petabytes of storage in a personal device.
CPU speeds of 100 times those we have now.
Wireless network bandwidth of 100 Gigabytes/Sec or mere.
This means that we can expect low power Internet tablets for less than a $1. These will be able to make free VoIP calls. Anywhere to Anywhere.
This is a world where in just 9 years, nearly everything will go online. I have already noted how FMCGs will have IP addresses and that even light globes are going online. The future is one where a simple embedded Linux controller will cost less than a cent for a 100 devices.
The digital divide is changing. Right now, only the rich nations have the necessary levels of access to the Internet and ecommerce. The future is one where even the poorest of countries will have complete access.
Think what this means for forensics. For privacy (or the end of).
MORE!
Start to think what this means for politics. In 10 years we will have low cost tablets. These will be disposable thin and easy to hide with access to the Internet. This is anywhere anytime. This will even mean access in places such as North Korea where Internet access is extremely restricted.
You may say that this will still pose an issue.
After all, the levels of literacy in many developing nations is low. Here is the rub, applications that talk to you are already available. SIRI is not new. I have been using Dragon Voice type for a decade now, but it is a CPU hog. Well, that is changing and these systems are improving. Further, I have “RealVoices” that offer a truly human sounding voice from the PC.
In 2020, we will have a future when any person anyplace on Earth can talk to any other person. This is instant translation of over 100 languages to any other. Of seeing text displayed on screen in any language from any language.
These are not idle claims, they are existing technologies that right now take large systems, but which in time (only a few years) will run on a device smaller than a watch.
Even in a nation as isolated and as poor as North Korea will see radical changes. Ask yourself what these device costs lead to. Think of the pamphlet drops we have seen in the past. In the future, it will cost less than it does to drop a piece of paper to drop a set of digital devices on a village.
Tablets that seem as if magic to the people who have been isolated from technology so long. Devices that will open the world, politics and learning to the poorest peoples on Earth.
Just imagine for a moment
Let your mind wander. For even with all I am saying, there is nothing I can state that will cover the changes, the fundamental differences that will develop from this by 2030. We are entering a new Era, a new world. There is no way to change this fact now, we have already past the point of no return.
Imagine for a moment in the coming years that you are that poor villager or peasant in North Korea. You have been isolated for your entire life. You have seen and heard little with only the doubts and false knowledge provided by your “leader”.
Now, suddenly a device is dropped in a crate from an airborne mission. Far too many at once for even a totalitarian regime to stop.
This device talks to you in your own language. It answer questions. It provides knowledge freely. It shows pictures and videos. Anything you ask.
You can see news, you can listen to speeches from the UN or movie stars in your own language (instantly translated).
You can access a wealth of classic books and if you cannot read these will be translated and read to you in your native dialect.
On Education
Think for a moment what this will be in regards to education. The existing school and University systems will be exposed to increasing competition. Not local competition any longer, but International. The best teachers will be able to teach from anywhere. I already have students in multiple countries.
In time, we will choose not from a small list of subjects offered in a local high school, but from a global collection and wealth of knowledge that is beyond my ability to contemplate fully. It is beyond any individuals power to truly grasp.
Add holographic technology.
Right now, personal projection technology is expensive, power hungry and available only to the rich. There are already companies creating virtual board rooms where the members are projected into a room they do not inhabit at the time. This is a 2.5 dimensional effect right now. A decade will change this. It will also make it simple and inexpensive. In the coming decade, projection devices will be a simple feature in phones. There are some already in development with this technology.
This is just a taste. I will write more on this topic. We have to start thinking and planning now for the future is coming. What we make of it will depend on how we act now. A decade is a very short time.
Posted by Craig Wright at Sunday, October 23, 2011
Labels: Awareness, Charles Sturt University
2 comments:
DXinfo said...
What if there is no internet in 10 years from now? :D No need for tablets, hard disks, and CPUs. How about having WW3 in 10 years because in 10 years from now, the world will see 2 more idiots as the President of USA? :D
Dr Craig S Wright GSE said...
Even idiots in the Presidency will not end the world so soon.
Source: archive.md/mqBJm#selection-4679.0-5130.0


BITCOIN-IS-WORSE-IS-BETTER
by gwern@gwern.net
27 May 2011
Bitcoin's long gestation and early opposition indicates it is an example of the 'Worse is Better' paradigm in which an ugly complex design with few attractive theoretical properties compared to purer competitors nevertheless successfully takes over a niche, survives, and becomes gradually refined.
Source:
https://www.gwern.net/Bitcoin-is-Worse-is-Better
10/19/2011 Bitcoin
Published by islandofawesome on 19 Oct 2011

LulzSec, Anonymous … freedom fighters or the new face of evil?
August 9, 2011
by Craig S Wright
PhD; Adjunct Lecturer in Computer Science, Charles Sturt University
As you’ll know by now, hacktivist group Anonymous has vandalised the home page of the Syrian Ministry of Defense, posting a message which started: “To the Syrian people: the world stands with you against the brutal regime of Bashar Al-Assad”.
The response from within Syria was swift, with the so-called “Syrian Electronic Army” retaliating by defacing Anonymous’s fledgling social network, Anon+.
So, was the backlash uncalled for?
Groups such as LulzSec and Anonymous have what many see as laudable goals.
They promote freedom, or at least they claim to. The real question in all this is: what constitutes freedom?
https://theconversation.com/lulzsec-anonymous-freedom-fighters-or-the-new-face-of-evil-2605

Real names
After reading Gavins thread on public relations, I wanted to find an easy way to make Bitcoin come across as a more professional, trustworthy project. I don't need to explain why that's an important image to establish.
So I changed my forum display name from [mike] to my real name, which was easily available from the BitCoinJ project anyway. Quite a few important players in the Bitcoin community aren't actually anonymous even though they use nicks on this forum. When people evaluate Bitcoins potential, one question they ask is, who are these people? Is anyone seriously standing behind this project? Just using our real names when posting is a simple step that will re-assure people who are deciding whether it's worth their time. So I encourage you to do the same - it's easy to do by going into the profile tab and clicking "Account Settings".
Here's a quick reference guide to some of the communities top contributors, based on publicly available information:
- Gavin Andresen, no need to introduce the project maintainer. He previously worked at Silicon Graphics and now runs his own company.
- MagicalTux - Mark Karpeles, owner of MtGox and Kalyhost
- Vladimir Marchenko, runs Marchenko Ltd which sells mining contracts, previously developed the figator.org search engine.
- xf2_org - Jeff Garzik, who does kernel development at Red Hat
- BlueMatt - Matt Corallo, core developer
- sipa - Pieter Wuille, core developer and maintainer of the network graphs
- justmoon - Stefan Thomas, creator of the WeUseCoins.com site/video and WebCoin.
- Hal - Hal Finney, one of the creators of PGP
- mndrix - Michael Hendrix, creator of the (sadly defunct) CoinPal and CoinCard services
- theymos - Michael Marquardt, creator of the widely used blockexplorer.com site
- genjix - Amir Taaki, creator of the Britcoin exchange
- Mike Hearn - Google engineer who works on Gmail and developed BitCoinJ
There are a few others I know based on private information. If you're OK with appearing here (or not appearing here) let me know.
BTW I know plenty of people posting in these forums prefer to be totally anonymous, and there's nothing wrong with that.
Bitcoin: $10,000 Bet that they will outperform Gold and Silver by 100X !!!
Published by wwwmemorydealerscom on 4 Aug 2011


Bitcoin Mt. Gox FLASH CRASH! Bitcoins at $0.01 Each
Published by BookofNick on 19 Jun 2011
Price crashes from $17.5 to $0.01. That i not a typo. ONE CENT.
Here is the official statement from Mt. Gox:
"The bitcoin will be back to around 17.5$/BTC after we rollback all trades that have happened after the huge Bitcoin sale that happened on June 20th near 3:00am (JST).
Service should be back by June 20th 11:00am (JST, 02:00am GMT) with all the trades reversed and accounts available.
One account with a lot of coins was compromised and whoever stole it (using a HK based IP to login) first sold all the coins in there, to buy those again just after, and then tried to withdraw the coins. The $1000/day withdraw limit was active for this account and the hacker could only get out with $1000 worth of coins.
Apart from this no account was compromised, and nothing was lost. Due to the large impact this had on the Bitcoin market, we will rollback every trade which happened since the big sale, and ensure this account is secure before opening access again."
This excuse is weak.
Try TRADE HILL INSTEAD: http://www.tradehill.com/?r=TH-R1323
Use referral code TH-R1323 when signing up at Trade HIll and get 10% off commissions for the life of your account.
1PzHtv94zW52fHSQGotogkhYibCcJM9LK5
Namecoin
1st fork of Bitcoin
18 April 2011
Unlike bitcoin, Namecoin can store data within its own blockchain transaction database. The original proposal for Namecoin called for Namecoin to insert data into bitcoin's blockchain directly.[7] Anticipating scaling difficulties with this approach,[8] a shared proof-of-work (POW) system was proposed to secure new cryptocurrencies with different use cases.[9]
Namecoin's flagship use case is the censorship-resistant top level domain .bit, which is functionally similar to .com or .net domains but is independent of ICANN, the main governing body for domain names.
Source:
https://en.wikipedia.org/wiki/Namecoin

February 23, 2011
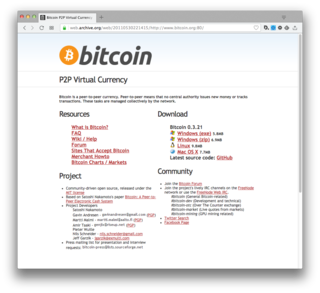
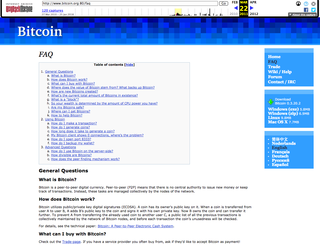
General Questions
What is Bitcoin?
Bitcoin is a peer-to-peer digital currency. Peer-to-peer (P2P) means that there is no central authority to issue new money or keep track of transactions. Instead, these tasks are managed collectively by the nodes of the network.
How does Bitcoin work?
Bitcoin utilizes public/private key digital signatures (ECDSA). A coin has its owner's public key on it. When a coin is transferred from user A to user B, A adds B’s public key to the coin and signs it with his own private key. Now B owns the coin and can transfer it further. To prevent A from transferring the already used coin to another user C, a public list of all the previous transactions is collectively maintained by the network of Bitcoin nodes, and before each transaction the coin’s unusedness will be checked.
For details, see the technical paper: Bitcoin: A Peer-to-Peer Electronic Cash System.
What can I buy with Bitcoin?
Check out the Trade-page. If you have a service provider you often buy from, ask if they'd like to accept Bitcoin as payment!
Where does the value of Bitcoin stem from? What backs up Bitcoin?
Bitcoins have value if they are accepted as payment by many.
When we say that a currency is backed up by gold, we mean that there's a promise in place that you can exchange the currency for gold. In a sense, you could say that Bitcoin is "backed up" by the price tags of merchants – a price tag is a promise to exchange goods for a specified amount of currency.
It's a common misconception that Bitcoins gain their value from the cost of electricity required to generate them. Cost doesn't equal value – hiring 1,000 men to shovel a big hole in the ground may be costly, but not valuable. Also, even though scarcity is a critical requirement for a useful currency, it alone doesn't make anything valuable. For example, your fingerprints are scarce, but that doesn't mean they have any exchange value.
How are new Bitcoins created?
New coins are generated by a network node each time it finds the solution to a certain calculational problem (i.e. creates a new block), for which an average solution time can be calculated. The difficulty of the problem is adjusted so that in the first 4 years of the Bitcoin network, 10,500,000 coins will be created. The amount is halved each 4 years, so it will be 5,250,000 in years 4-8, 2,625,000 in years 8-12 and so on. Thus the total number of coins will approach 21,000,000 over time.
What's the current total amount of Bitcoins in existence?
The number of blocks times the coin value of a block. The coin value is 50 bc per block for the first 210,000 blocks, 25 bc for the next 210,000 blocks, then 12.5 bc, 6.25 bc and so on.
As of October 30th 2009, there are about 26,000 blocks in the block chain, which means 26,000 * 50 bc = 1,300,000 bitcoins in existence. You can see the up-to-date number of blocks in the status bar of the Bitcoin main window.
What is a "block"?
A block is a unit which contains the information of the transactions made after the previous block, plus a transaction which assigns a new coin to the creator of the block. Blocks form a chain from the first block to the latest block. To create a new block you need to spend CPU time, which acts as an unbribable timestamp for the previous transactions. The average rate of block creation in the whole system is 6 / hour. For details, see the technical paper: Bitcoin: A Peer-to-Peer Electronic Cash System.
The block chain length is shown in the status bar of the Bitcoin main window. The number increases rapidly while your Bitcoin client is downloading the block chain from other nodes. After the downloading is finished, your node can start generating new blocks.
So your wealth is determined by the amount of CPU power you have?
No. There's a constant average rate of new Bitcoins created, and that amount is divided among the nodes by the CPU power they supply. The competition for coin creation will drive the price of electricity needed for generating a coin close to the value of the coin, so the profit margin won't be that huge. The easier way to gain a lot of wealth would be trading goods.
At the moment, though, you can generate new coins quite profitably, if you expect them to have real value in the future. If you choose to, be aware that Bitcoin is still experimental software.
Are my Bitcoins safe?
As long as you make backups of your Bitcoin wallet, protect it with a strong password and keep keyloggers away from your computer. You need to make a backup of your wallet after each transaction, as the old wallet backup will be partially or completely invalid.
If you lose your wallet or if some unknown attacker gets it and manages to break your password, there’s no way to get your coins back. On the other hand, that is usually also the case if you lose your physical wallet.
Where can I get Bitcoins?
Find a Bitcoin owner and sell her something - MMORPG equipment, IT support, lawn mowing, dollars or whatever you can trade with her. You can also generate new Bitcoins for yourself by running a Bitcoin network node.
You can find currency exchangers on the Trade page.
How to help Bitcoin?
You can:
- offer Bitcoin as a payment option at your web shop or service
- tell about Bitcoin to people who might be interested
- translate Bitcoin to your language if it isn't already here
- write documentation on the wiki
- report bugs, help people and discuss Bitcoin on the forum
- help people, or just chat in the irc channel with your own client if you have one, or use the official Freenode webclient here
Using Bitcoin
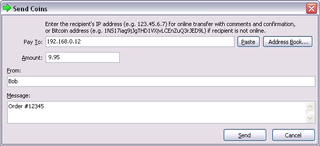
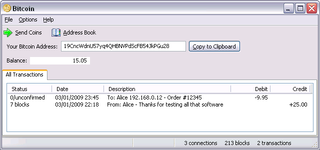
How do I make a transaction?
When you want to send coins, click the ''Send Coins'' button up in the main window. You can send coins to the recipient's IP address if he's running the Bitcoin client, or to his Bitcoin address even if he's not online or doesn't want to reveal his IP. A comment can be included when sending to an IP.
If you're receiving a valuable amount of coins from a sender whom you can't be sure to trust, before accepting the transaction you may want to wait until it's verified by a few blocks. The more blocks you wait, the closer to zero is the sender's chance to successfully double-spend the coins sent to you. The amount of blocks after the transaction is shown in the ''Status'' column of the transaction list in the main window.
How do I generate coins?
Turn on ''Options -> Generate Coins'' to run a node and generate new coins. Be sure to have port 8333 open for incoming connections (instructions).
How long does it take to generate a coin?
Initially your Bitcoin client will have to download and verify the Bitcoin block chain, which is indicated by the number of blocks (shown in the status bar) increasing rapidly. On a modern PC that might take a few hours, after which it will start generating coins.
Your average coin creation rate will be (6 * 50 coins / hour) * (your CPU speed / the total CPU speed in the Bitcoin network). At the moment (December 2010) it would take a year on average to generate 50 coins with a typical PC. You can get an estimation of your block generation rate here.
My Bitcoin client shows 0 connections, where’s the problem?
That could happen if port 8333 is not open for incoming connections (instructions).
How do I open port 8333?
If you’re behind a firewall, it will usually ask if you want to allow incoming connections to an application when running it for the first time. If you’re also behind NAT, see www.portforward.com for instructions how to forward the port correctly. Select your router from the list and see its Default Guide.
Use www.canyouseeme.org to check if the port is accepting incoming connections.
How do I backup my wallet?
Your wallet.dat is stored in the directory ''%appdata%\Bitcoin'', which is typically:
Windows XP:
C:\Documents and Settings\username\Application Data\Bitcoin
Windows Vista:
C:\Users\username\AppData\Roaming\Bitcoin
Linux:
~/.bitcoin
You need to make a backup of the wallet after every transaction, as the old backup file will be partially or fully invalid. Wait at least a few seconds after your last transaction before making the backup.
If you want to encrypt your backup, you can use some program like TrueCrypt. An in-built tool for encrypting your wallet will be included in Bitcoin later on.
Advanced Questions
How do I use Bitcoin on the server-side?
Run bitcoin with switch -server or use the Bitcoin daemon (bitcoind) supplied with the download package. Bitcoin has an API that can be used via command line or JSON-RPC. The API documentation can be found in the wiki.
How divisible are Bitcoins?
Technically, a Bitcoin can be divided down to 8 decimals, so 0.00000001 BTC is the smallest possible amount. For convenience, the program currently accepts only 2 decimal places.
How does the peer finding mechanism work?
Bitcoin finds peers primarily by connecting to an IRC server (channel #bitcoin on irc.lfnet.org). If a connection to the IRC server cannot be established (like when connecting through TOR), an in-built node list will be used and the nodes will be queried for more node addresses.
Source: archive.org
Re: Bitcent?
February 18, 2011, 08:50:57 AM
marcus_of_augustus
1 satoshi = 1 microbitcent (smallest denomination)
100 million satoshis = 1 bitcoin
Are we agreed?
February 18, 2011, 10:51:26 AM
no to the gold cult
Affirmative.
Satoshi (unit)
https://en.bitcoin.it/wiki/Satoshi_(unit)


Published on eff.org on January 20th, 2011
Bitcoin - a Step Toward Censorship-Resistant Digital Currency
Commentary by Rainey Reitman
A few weeks ago, we mentioned rather unusual technological endeavor to create an online currency. We received a few queries about this subject, so decided to provide a more thorough description of what digital currency is, how this system works, why it's appealing and how it might fall short of user expectations.
To understand digital currency, one must first note that money in the digital age has moved from a largely anonymous system to one increasingly laden with tracking, control and regulatory overhead. Our cold hard cash is now shepherded through a series of regulated financial institutions like banks, credit unions and lenders. Bitcoin, created in 2009 by Satoshi Nakamoto, is a peer-to-peer digital currency system that endeavors to re-establish both privacy and autonomy by avoiding the banking and government middlemen. The goal is to allow individuals and merchants to generate and exchange modern money directly. Once the Bitcoin software has been downloaded, a user can store Bitcoins and exchange them directly with other users or merchants — without the currency being verified by a third party such as a bank or government. It uses a unique system to prevent multiple-spending of each coin, which makes it an interesting development in the movement toward digital cash systems.
The model proposed by Bitcoin is in many ways a response to some of the privacy and autonomy concerns surrounding our current financial system. Current money systems now increasingly come with monitoring of financial transactions and blocking of financial anonymity. A peer-to-peer currency could theoretically offer an alternative to the bank practices that increasingly include sharing information on their customers who don't actively opt-out, and who may even then be able to share data with affiliates and joint marketers. Bitcoin is particularly interesting in the wake of recent events that demonstrated how financial institutions can make political decisions in whom they service, showcased by the decisions of PayPal, Visa, Mastercard and Bank of America to cut off services to Wikileaks. Bitcoin, if it were to live up to the dreams of its creators, might offer the kind of anonymity and freedom in the digital environment we associate with cash used in the offline world.
But Bitcoin's current implementation won't resolve all of the issues surrounding autonomy and privacy. Notably, the anonymity on Bitcoin is not entirely secure at this time, which makes its merits as a more private form of currency tenuous at best. There are also other weaknesses to the system, some significant, which should be understood before using Bitcoin. And as of this writing, Bitcoin can't be used to donate to Wikileaks. But even more important than these concerns is the fact that governments around the world may raise legal issues with any digital cash scheme — ranging from money laundering to tax evasion to a range of other regulatory concerns. Nonetheless, Bitcoin is an intriguing project and worth watching to see how it develops in the coming years.
While Bitcoin is relatively young, digital currencies have been around a long time. Digicash, released in 1994, is considered a pioneer of electronic cash using cryptography to maintain anonymity. The Ripple currency project relies on interpersonal relationships to allow communities to create their own money systems (which is similar to the Local Exchange Trading System). There is also the anonymous digital cash system eCache, which can only be accessed via the anonymous onion routing network Tor. There are also numerous other digital money projects that have been proposed over the years; Bitcoin is just the newest chapter in the ongoing effort to create wholly digital currency.
Bitcoin is not challenging to use. Anyone can go online and start generating Bitcoins. The computer creates a coin by dedicating CPU power to solving a mathematical problem; every time the problem is solved, a Bitcoin is generated and another problem is offered up. The total number of Bitcoins will approach 21,000,000 over time. Learn more.
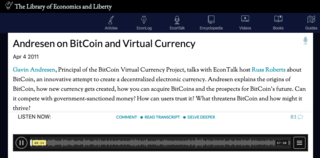
Perhaps the most interesting dimension of the Bitcoin project is its unorthodox approach to fraud prevention. Traditional currency systems have relied on trusted third parties to verify that the same unit of currency is not exchanged multiple times. For example, when you make a purchase with your credit card, the credit card company adjusts your available balance. Bitcoin addresses this problem without a third party by making all transactions public. As Bitcoin developer Gavin Andresen explained, every coin has a digital signature attached to it for every transaction that takes place; each time the coin is exchanged, another signature is added. If two coins appear identical, the one that was accepted by the Bitcoin network first is considered valid. Even though the transactions are public, the individuals tied to the transactions are anonymous. This is similar to how the stock exchange makes stock values public without disclosing individual owners. See the technical paper: Bitcoin: a Peer-to-Peer Electronic Cash System.
It's too early to say whether Bitcoin will be a success. Any new currency system faces an uphill battle, both technically and legally. The worth of Bitcoins, if the system ever gets wide adoption, will be based on an ever-fluctuating market value. Merchants will need to accept Bitcoins as a placeholder for goods and services, just like any other form of currency. This has been a barrier to other digital cash options historically, so it's difficult to know whether Bitcoin will be better prepared to face these challenges. But many believe that there's a need for decentralized currency system, and Bitcoin certainly is a step toward censorship-resistant digital currency. Bitcoins can already be used to make purchases and can even be donated to a few of your favorite charities — including EFF.
Related Issues: Anonymity, Privacy
Source: eff.org


From: Mike Hearn mike@plan99.net Date: Mon, Dec 27, 2010 at 8:21 PM To: Satoshi Nakamoto satoshin@gmx.com
Happy Christmas Satoshi, assuming you celebrate it wherever you are in the world :-)
I have been working on a Java implementation of the simplified payment verification, with an eye to building a client that runs on Android phones. So I've been thinking a lot about storage requirements and the scalability of BitCoin, which led to some questions that the paper did not answer (maybe there could be a new version of the paper at some point, as I think aspects of it are now out of date).
Specifically, BitCoin has a variety of magic numbers and neither the code nor the paper explain where they came from. For example, the fact that inflation ceases when 21 million coins have been issued. This number must have been arrived at somehow, but I can't see how.
Another is the 10 minute block target. I understand this was chosen to allow transactions to propagate through the network. However existing large P2P networks like BGP can propagate new data worldwide in <1 minute.
The final number I'm interested in is the 500kb limit on block sizes. According to Wikipedia, Visa alone processed 62 billion transactions in 2009. Dividing through we get an average of 2000 transactions per second, so peak rate is probably around double that at 4000 transactions/sec. With a ten minute block target, at peak a block might need to contain 2.4 million transactions, which just won't fit into 500kb. Is this 500kb a temporary limitation that will be slowly removed over time from the official client or something more fundamental?
From: Satoshi Nakamoto <satoshin@gmx.com>
Date: Wed, Dec 29, 2010 at 10:42 PM
To: Mike Hearn <mike@plan99.net>
The simplified payment verification in the paper imagined you would receive transactions directly, as with sending to IP address which nobody uses, or a node would index all transactions by public key and you could download them like downloading mail from a mail server.
Instead, I think client-only nodes should receive full blocks so they can scan them for their own transactions. They don't need to store them or index them. For the initial download, they only need to download headers, since there couldn't be any payments before the first time the program was run (a header download command was added in 0.3.18). From then on, they download full blocks (but only store the headers).
Code for client-only mode is mostly implemented. There's a feature branch on github with it, also I'm attaching the patch to this message.
Read on
Source:
https://pastebin.com/wA9Jn100

BLOG | ELECTRONIC FRONTIER FOUNDATION
December 14th, 2010
Constructive Direct Action Against Censorship
Call To Action by Chris Palmer
The past few weeks have highlighted the vulnerability of centralized information systems to censorship: online speech is only as strong as the weakest intermediary. Sites hosting legitimate speech were caught up in an anti-counterfeiting raid by the Department of Homeland Security, EveryDNS stopped hosting WikiLeaks.org’s DNS, Amazon refused hosting service to WikiLeaks, and independent protesters conducted denial-of-service attacks on businesses refusing service to WikiLeaks. If the Combating Online Infringements and Counterfeits Act (COICA; the internet censorship bill introduced in the US Senate) or something like it passes, the threat centralization poses to First Amendment-protected speech may be unavoidable. Corrective action — designing, implementing, and deploying robust, fault-tolerant architectures — will improve the security and availability of the internet infrastructure generally, to the benefit of all.
What, then, can digital activists do to protect speech on the internet? Fortunately, there are a bunch of technical projects dedicated to reducing centralization in the internet infrastructure. Some are in the idea stage, some are up and running, and some are in-between. All of them could use help: development, documentation, security review, server infrastructure, testing, and evangelizing. EFF urges technologists of all stripes and skill levels to work on potential solutions to the centralization problem.
In this post I’ll summarize a few interesting projects, but this list is hardly exhaustive.
The Dot-P2P Project, an alternative DNS hierarchy that resists censorship. The project aims to create a new top-level domain, .p2p, and name-resolution software that will hook into the normal client DNS resolver. (However, the new software will not interfere with name resolution for traditional TLDs like .com and .net.) Dot-p2p developers expect the .p2p service infrastructure to be mobile and hence flexible under attack; by contrast, administration is currently expected to be centralized. However, the developers would like to see a design for decentralized administration as well.
The Tahoe Least-Authority File System, a highly fault-tolerant, secure internet filesystem. Historically, network filesystems such as SMB/CIFS and NFS have been both centralized (having a single server) and insecure (lacking any authentication, confidentiality, or integrity for the data). Previous work, such as The Coda Filesystem and Mazières’ SFS, has attempted to address these problems. Tahoe-LAFS is a new effort in this area with an innovative, fine-grained internet-strength security model. Tahoe-LAFS could be used as the basis for a censorship-resistant, confidential, tamper-resistant publishing platform. Transported over Tor, it could also be anonymous.
The Tor Project, an anonymizing overlay network. Although better-known than the other projects described in this post, Tor remains a fruitful project to work on and there is plenty of work left to do. In particular, the use of Tor hidden services lags behind the use of Tor on the client side for many reasons, including performance and the need for more server infrastructure. And to help defeat censorship systems, there is always a need for more people run Tor Bridge Relays.
BitCoin, a decentralized internet currency. Digital cash systems, usually based on cryptographic “proof of work” schemes, have been around since 1990. Some digital cash systems are anonymous or pseudonymous (using e.g. Chaum’s blind signatures), but not all are. Historically, digital cash systems have not succeeded; BitCoin is a new attempt that may be promising. You can download and run the code now, and you can indeed buy things with BitCoins.
It may be that some or all of these projects do not succeed, or succeed only partially. That is to be expected — decentralizing and hardening the internet infrastructure and applications against censorship is an ongoing research and development project. The only way to progress is gradually and with effort, but the payoff could be huge.
Related Issues: Free Speech, The COICA Internet Censorship and Copyright Bill, Wikileaks
Source: eff.org
"Digital cash systems, usually based on cryptographic “proof of work” schemes, have been around since 1990. Some digital cash systems are anonymous or pseudonymous (using e.g. Chaum’s blind signatures), but not all are. Historically, digital cash systems have not succeeded; BitCoin is a new attempt that may be promising. You can download and run the code now, and you can indeed buy things with BitCoins."
—Chris Palmer (eff.org)

Bitcoin and the EFF.
Published by Bitcoin Poet on 15 Nov 2010
http://bitcoinpoet.com Bitcoin Punographer
18LtJy9sWMBMChfSYVJBi9FUsuL3YaeSyW
November 27, 2010
General Questions
What is Bitcoin?
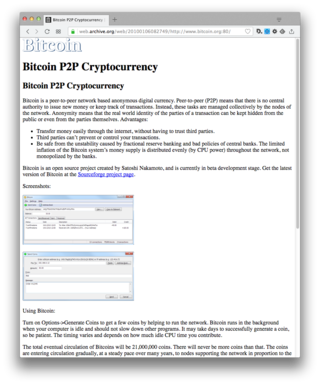
Bitcoin is a peer-to-peer network based anonymous digital currency. ''Peer-to-peer'' (P2P) means that there is no central authority to issue new money or to keep track of the transactions. Instead, those tasks are managed collectively by the nodes of the network. ''Anonymity'' means that the real world identity of the parties of a transaction can be kept hidden from the public or even from the parties themselves.
How does Bitcoin work?
Bitcoin utilizes public/private key cryptography. A coin has its owner's public key on it. When a coin is transfered from user A to user B, A adds B’s public key to the coin and signs it with his own private key. Now B owns the coin and can transfer it further. To prevent A from transferring the already used coin to another user C, a public (but anonymous) list of all the previous transactions is collectively maintained by the network of Bitcoin nodes, and before each transaction the coin’s unusedness will be checked.
For details, see the technical paper: Bitcoin: A Peer-to-Peer Electronic Cash System.
What can I buy with Bitcoin?
Check out the Trade-page. If you have a service provider you often buy from, we really appreciate if you can ask if they'd like to accept Bitcoin as payment!
Where does the value of Bitcoin stem from? What backs up Bitcoin?
Bitcoin has value because it is accepted as payment by many. The initial market value was achieved when people speculated, that because of its properties, the currency would be accepted by others later on.
When we say that a currency is backed up by gold, we mean that there's a promise in place that you can exchange the currency for gold. In a sense, you could say that Bitcoin is "backed up" by the price tags of merchants and currency exchangers – a price tag is a promise to exchange goods for a specified amount of currency. Of course, price tags may or may not be as long-term promises as those made by central banks or governments.
It's a common misconception that Bitcoins gain their value from the cost of electricity required to generate them. Cost doesn't equal value – hiring 1,000 men to shovel a big hole in the ground may be costly, but not valuable. Also, even though scarcity is a critical requirement for a useful currency, it alone doesn't make anything valuable. Your fingerprints are scarce, but that doesn't mean they have any exchange value.
How are new Bitcoins created?
New coins are generated by a network node each time it finds the solution to a certain calculational problem (i.e. creates a new block), for which an average solution time can be calculated. The difficulty of the problem is adjusted so that in the first 4 years of the Bitcoin network, 10,500,000 coins will be created. The amount is halved each 4 years, so it will be 5,250,000 in years 4-8, 2,625,000 in years 8-12 and so on. Thus the total number of coins will approach 21,000,000 over time.
What's the current total amount of Bitcoins in existence?
The number of blocks times the coin value of a block. The coin value is 50 bc per block for the first 210,000 blocks, 25 bc for the next 210,000 blocks, then 12.5 bc, 6.25 bc and so on.
As of October 30th 2009, there are about 26,000 blocks in the block chain, which means 26,000 * 50 bc = 1,300,000 bitcoins in existence. You can see the up-to-date number of blocks in the status bar of the Bitcoin main window.
What is a "block"?
A block is a unit which contains the information of the transactions made after the previous block, plus a transaction which assigns a new coin to the creator of the block. Blocks form a chain from the first block to the latest block. To create a new block you need to spend CPU time, which acts as an unbribable timestamp for the previous transactions. The average rate of block creation in the whole system is 6 / hour. For details, see the technical paper: Bitcoin: A Peer-to-Peer Electronic Cash System.
The block chain length is shown in the status bar of the Bitcoin main window. The number increases rapidly while your Bitcoin client is downloading the block chain from other nodes. After the downloading is finished, your node can start generating new blocks.
So your wealth is determined by the amount of CPU power you have?
No. There's a constant average rate of new Bitcoins created, and that amount is divided among the nodes by the CPU power they use. When Bitcoins start having real exchange value, the competition for coin creation will drive the price of electricity needed for generating a coin close to the value of the coin, so the profit margin won't be that huge. The easier way to gain a lot of wealth would be trading goods.
At the moment, though, you can generate new coins quite profitably, if you expect them to have real value in the future. If you choose to, be aware that Bitcoin is still experimental software.
Is Bitcoin safe?
Yes, as long as you make backups of your Bitcoin wallet, protect it with a strong password and keep keyloggers away from your computer. You need to make a backup of your wallet after each transaction, as the old wallet backup will be partially or completely invalid.
If you lose your wallet or if some unknown attacker gets it and manages to break your password, there’s no way to get your coins back. On the other hand, that is usually also the case if you lose your physical wallet.
Why should I use Bitcoin?
- Transfer money easily through the Internet, without having to trust middlemen.
- Third parties can’t prevent or control your transactions.
- Bitcoin transactions are practically free, whereas credit cards and online payment systems typically cost 1-5% per transaction plus various other fees up to hundreds of dollars.
- Be safe from the instability caused by fractional reserve banking and bad policies of the central banks. The limited inflation of the Bitcoin system’s money supply is distributed evenly (by CPU power) throughout the network, not monopolized to the banks.
Where can I get Bitcoins?
Find a Bitcoin owner and sell her something - MMORPG equipment, IT support, lawn mowing, dollars or whatever you can trade with her. You can also generate new Bitcoins for yourself by running a Bitcoin network node.
You can find currency exchangers on the Trade page.
How to help Bitcoin?
You can:
- offer Bitcoin as a payment option at your web shop or service
- tell about Bitcoin to people who might be interested
- translate Bitcoin to your language if it isn't already here
- write documentation on the wiki
- report bugs, help people and discuss Bitcoin on the forum
- help people, or just chat in the irc channel with your own client if you have one, or use the official Freenode webclient here
Using Bitcoin
How do I make a transaction?
When you want to send coins, click the ''Send Coins'' button up in the main window. You can send coins to the recipient's IP address if he's running the Bitcoin client, or to his Bitcoin address even if he's not online or doesn't want to reveal his IP. A comment can be included when sending to an IP.
If you're receiving a valuable amount of coins from a sender whom you can't be sure to trust, before accepting the transaction you may want to wait until it's verified by a few blocks. The more blocks you wait, the closer to zero is the sender's chance to successfully double-spend the coins sent to you. The amount of blocks after the transaction is shown in the ''Status'' column of the transaction list in the main window.
How do I generate coins?
Turn on ''Options -> Generate Coins'' to run a node and generate new coins. Be sure to have port 8333 open for incoming connections (instructions).
How long does it take to generate a coin?
Initially your Bitcoin client will have to download and verify the Bitcoin block chain, which is indicated by the number of blocks (shown in the status bar) increasing rapidly. On a modern PC that might take a few hours, after which it will start generating coins.
Your average coin creation rate will be (6 * 50 coins / hour) * (your CPU speed / the total CPU speed in the Bitcoin network). At the moment (August 2010) it might be something like 50 coins / 3 weeks, for example.
My Bitcoin client shows 0 connections, where’s the problem?
That could happen if port 8333 is not open for incoming connections (instructions).
How do I open port 8333?
If you’re behind a firewall, it will usually ask if you want to allow incoming connections to an application when running it for the first time. If you’re also behind NAT, see www.portforward.com for instructions how to forward the port correctly. Select your router from the list and see its Default Guide.
Use www.canyouseeme.org to check if the port is accepting incoming connections.
How do I backup my wallet?
Your wallet.dat is stored in the directory ''%appdata%\Bitcoin'', which is typically:
Windows XP:
C:\Documents and Settings\username\Application Data\Bitcoin
Windows Vista:
C:\Users\username\AppData\Roaming\Bitcoin
Linux:
~/.bitcoin
You need to make a backup of the wallet after every transaction, as the old backup file will be partially or fully invalid. Wait at least a few seconds after your last transaction before making the backup.
If you want to encrypt your backup, you can use some program like TrueCrypt. An in-built tool for encrypting your wallet will be included in Bitcoin later on.
Advanced Questions
How do I use Bitcoin on the server-side?
Run bitcoin with switch -server or use the Bitcoin daemon (bitcoind) supplied with the download package. Bitcoin has an API that can be used via command line or JSON-RPC. The API documentation can be found in the wiki.
How divisible are Bitcoins?
Technically, a Bitcoin can be divided down to 8 decimals, so 0.00000001 BTC is the smallest possible amount. For convenience, the program currently accepts only 2 decimal places.
How does the peer finding mechanism work?
Bitcoin finds peers primarily by connecting to an IRC server (channel #bitcoin on irc.lfnet.org). If a connection to the IRC server cannot be established (like when connecting through TOR), an in-built node list will be used and the nodes will be queried for more node addresses.
Source: archive.org
Block: 62499
"I don't care."
The iPhone 4 was released on June 24, 2010, in the United States, United Kingdom, France, Germany, and Japan.
24 Jun 2010
Source: youtube.com

Bitcoin Technical Analysis
Published by Bitcoin Poet on 15 Nov 2010
http://bitcoinpoet.com
18LtJy9sWMBMChfSYVJBi9FUsuL3YaeSyW
Poll:
Which symbol do you like best?
฿ - 200 (42.2%)
ⓑ - 35 (7.4%)
Ⓑ - 68 (14.3%)
Ƀ - 96 (20.3%)
¤ - 1 (0.2%)
None of the above - 74 (15.6%)
Total Voters: 470
Source: bitcointalk.org
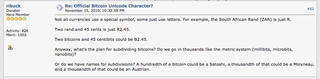
Re: Official Bitcoin Unicode Character?
https://bitcointalk.org/index.php?topic=369.msg22160#msg22160
The first recorded exchange rate was 1309 BTC per USD

How I Met Satoshi
Published by Jon Matonis on May 2, 2016
My relationship with the individual known as Satoshi Nakamoto started in early March 2010 when I received an email from Satoshi pointing me to the published Bitcoin white paper and encouraging me to investigate the system and to begin promoting the network by transacting and mining. At the time, I managed a digital currency blog and this was an email relationship with some brief correspondence.
[...]
Source:
https://medium.com/@jonmatonis/how-i-met-satoshi-96e85727dc5a
Cracked, inSecure and Generally Broken
The ravings of a SANS/GIAC GSE (Compliance & Malware) Security, Digital Forensics Statistics and Data Mining. I mined Bitcoin in the past and write code.
www.gse-compliance.blogspot.com


"Since 2007. At some point I became convinced there was a way to do this without any trust required at all and couldn't resist to keep thinking about it. Much more of the work was designing than coding."
Posted by satoshi on June 18, 2010, 04:17:14 PM on bitcointalk.org
Re: Transactions and Scripts: DUP HASH160 ... EQUALVERIFY CHECKSIG
published by Satoshi Nakamoto at Bitcointalk forum
The nature of Bitcoin is such that once version 0.1 was released, the core design was set in stone for the rest of its lifetime.
Because of that, I wanted to design it to support every possible transaction type I could think of. The problem was, each thing required special support code and data fields whether it was used or not, and only covered one special case at a time. It would have been an explosion of special cases. The solution was script, which generalizes the problem so transacting parties can describe their transaction as a predicate that the node network evaluates. The nodes only need to understand the transaction to the extent of evaluating whether the sender's conditions are met.
The script is actually a predicate. It's just an equation that evaluates to true or false. Predicate is a long and unfamiliar word so I called it script.
The receiver of a payment does a template match on the script. Currently, receivers only accept two templates: direct payment and bitcoin address. Future versions can add templates for more transaction types and nodes running that version or higher will be able to receive them. All versions of nodes in the network can verify and process any new transactions into blocks, even though they may not know how to read them.
The design supports a tremendous variety of possible transaction types that I designed years ago. Escrow transactions, bonded contracts, third party arbitration, multi-party signature, etc. If Bitcoin catches on in a big way, these are things we'll want to explore in the future, but they all had to be designed at the beginning to make sure they would be possible later.
I don't believe a second, compatible implementation of Bitcoin will ever be a good idea. So much of the design depends on all nodes getting exactly identical results in lockstep that a second implementation would be a menace to the network. The MIT license is compatible with all other licenses and commercial uses, so there is no need to rewrite it from a licensing standpoint.

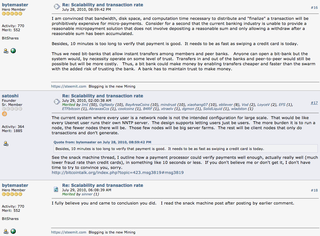

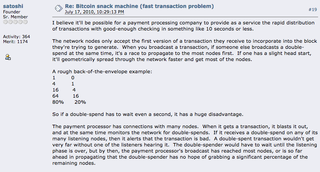
Re: Scalability and transaction rate
"The current system where every user is a network node is not the intended configuration for large scale. That would be like every Usenet user runs their own NNTP server. The design supports letting users just be users. The more burden it is to run a node, the fewer nodes there will be. Those few nodes will be big server farms. The rest will be client nodes that only do transactions and don't generate." —satoshi
Discussion between Daniel Larimer and Satoshi Nakamoto, July 28-29, 2010
Source:
https://bitcointalk.org
Craig S Wright
"Instead of the supply changing to keep the value the same, the supply is predetermined and the value changes. As the number of users grows, the value per coin increases. It has the potential for a positive feedback loop; as users increase, the value goes up"
Satoshi Nakamoto, 2009
What is meant by an online community and how is it important for e-commerce
Posted by Craig Wright at Saturday, April 25, 2009
I usually shy away from
Wikipedia as the democratization of knowledge does not make something true. Where many people hold a fallacy, it gets propagated in a Wiki. It is a basis of art and not science. Art has a place, but I prefer to hold to scientific principles and test knowledge. I like to have a quantitative basis for the truth that is greater than the sum of how many people believe.
However, in this instance, I feel that it is appropriate to take my first quote from just that source (Wikipedia).
A virtual community, e-community or online community is a group of people that primarily interact via communication media such as newsletters, telephone, email, internet social network service or instant messages rather than face to face, for social, professional, educational or other purposes. If the mechanism is a computer network, it is called an online community.So the question is, what does this really mean?
Online communities open up global opportunities while also increasing the volume of information available to consumers. Adam Smith postulated the ideal free market in “The Wealth of Nations” (Smith, 1776). The “invisible hand” of this free-market ideal is closer with the formation of open global communities for those who have a part within them. The failing remains the lack of complete knowledge with many parties facing an increasingly diverse “digital Divide” (NITA, 1995).
The growth of these communities has aided both Altruism and Envy (Konrad, 2002) with the development of positive and negative causes. It is noted that in economic terms, the utility value of these strategies results in the situation where “altruistic or envious individuals should achieve a lower expected material payoffs than individuals who are not altruistic or envious”. This is of course reflective of the physical world, with the projection of human desires and needs into the virtualised. These communities if stable could produce a socio-evolutionary march towards economic equilibrium.
The fallacy with the former statement is that no online community is close to achieving constancy. The growth of Internet based communities as more people are introduced radically alters the balance and mix of these communities. In addition, the developed countries are approaching a saturation point where large numbers of the population are online. Conversely, developing countries are (although fractionally slower in growth) adding more people to this global mix. The larger population densities in many of these countries mean that they will radically shift the Internet distribution away from homeostasis for many years to come.
An additional issue is the opportunity for free-riders in Internet communities. It has been stated that “on the Internet, nobody knows you are a dog” (Steiner, 1996).

The ability to hide on the Internet makes many people wary of using the Internet for commerce. Digital forensics can help. Making people accountable is a key factor in commercial transactions, both virtual and physical.
Although in development, online communities (such as
Linked-In) have aided in creating a reputation structure where people can uncover the details needed to find enough information to be able to develop trust. This again is
far from perfect with many failures. Again, we are in the development phase and far from equilibrium.
The absence of fraud remains a stumbling block. Market activity (commerce) can only be deemed to be truly voluntary and contain free activity if those who make it engage it knowingly. Smith's perfect market has to provide everyone with exactly what they expect. This market assumes perfect knowledge by all the parties. This requires an absence of fraud.
A lack of security and more crucially an near absence of globally enforceable laws and other legislative frameworks is arguably the greatest block to such a process. Until we can increase security and trust in the online communities we engage in, we can not create a truly open market. Security will never be enforceable without a suitable global legislative framework.
So we remain in the wild wild web for the time being.
Source:
ITC565 Developer's Blog
New icons, what do you think? Better than the old one?




Full size 530x529 image for scaling down to custom sizes:
http://www.bitcoin.org/download/bitcoin530.pngThe perspective shadow was too thick on the larger sizes. I updated 32, 48 and the full size.
I release these images into the public domain (copyright-free). I request that derivative works be made public domain.


Ron Lynam
Posted by Craig Wright at Friday, June 19, 2009
Last night my grandfather died at the age of 93. This follows a long battle with Parkinson's disease.
He will be sorely missed by family and friends.
My grandfather was an electronics expert and engineer in the early days of this discipline. It was through him I gained a love and passion for computers and electronics. It was because of him that I first learnt to program. He taught me Assembly and C (which at the time I generally used to reverse engineer games such that my sisters could never win).
It was through him that I obtained my first Unix terminal account on a dial up modem (75/300 baud) in 1979. As a consequence, it is him I owe my current career to.
Pop, I will miss you.
Source: Cracked, inSecure and Generally Broken
Integyrs produces a comprehensive cryptographic and mathematical library or objects for scientific, statistical, engineering and network code development.
Integyrs Pty Ltd (ACN 137 033 535)
Source:
www.integyrs.com
Posted by Satoshi Nakamoto on February 11, 2009 at 22:27
I've developed a new open source P2P e-cash system called Bitcoin. It's completely decentralized, with no central server or trusted parties, because everything is based on crypto proof instead of trust. Give it a try, or take a look at the screenshots and design paper:
Download Bitcoin v0.1 at http://www.bitcoin.org
The root problem with conventional currency is all the trust that's required to make it work. The central bank must be trusted not to debase the currency, but the history of fiat currencies is full of breaches of that trust. Banks must be trusted to hold our money and transfer it electronically, but they lend it out in waves of credit bubbles with barely a fraction in reserve. We have to trust them with our privacy, trust them not to let identity thieves drain our accounts. Their massive overhead costs make micropayments impossible.
A generation ago, multi-user time-sharing computer systems had a similar problem. Before strong encryption, users had to rely on password protection to secure their files, placing trust in the system administrator to keep their information private. Privacy could always be overridden by the admin based on his judgment call weighing the principle of privacy against other concerns, or at the behest of his superiors. Then strong encryption became available to the masses, and trust was no longer required. Data could be secured in a way that was physically impossible for others to access, no matter for what reason, no matter how good the excuse, no matter what.
It's time we had the same thing for money. With e-currency based on cryptographic proof, without the need to trust a third party middleman, money can be secure and transactions effortless.
One of the fundamental building blocks for such a system is digital signatures. A digital coin contains the public key of its owner. To transfer it, the owner signs the coin together with the public key of the next owner. Anyone can check the signatures to verify the chain of ownership. It works well to secure ownership, but leaves one big problem unsolved: double-spending. Any owner could try to re-spend an already spent coin by signing it again to another owner. The usual solution is for a trusted company with a central database to check for double-spending, but that just gets back to the trust model. In its central position, the company can override the users, and the fees needed to support the company make micropayments impractical.
Bitcoin's solution is to use a peer-to-peer network to check for double-spending. In a nutshell, the network works like a distributed timestamp server, stamping the first transaction to spend a coin. It takes advantage of the nature of information being easy to spread but hard to stifle. For details on how it works, see the design paper at http://www.bitcoin.org/bitcoin.pdf
The result is a distributed system with no single point of failure. Users hold the crypto keys to their own money and transact directly with each other, with the help of the P2P network to check for double-spending.
Satoshi Nakamoto
http://www.bitcoin.org
Original post:
http://p2pfoundation.ning.com/forum/topics/bitcoin-open-source
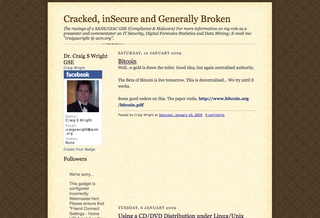
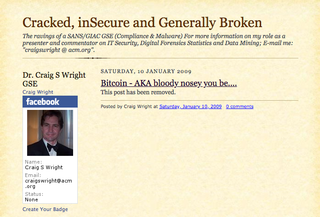
AN ARCHIVED COPY OF A NOW-DELETED BLOG POST FROM WRIGHT DATED JANUARY 10, 2009, WHICH READS: “THE BETA OF BITCOIN IS LIVE TOMORROW. THIS IS DECENTRALIZED… WE TRY UNTIL IT WORKS.” (THE POST WAS DATED JANUARY 10, 2009, A DAY AFTER BITCOIN’S OFFICIAL LAUNCH ON JANUARY 9TH OF THAT YEAR. BUT IF WRIGHT, LIVING IN EASTERN AUSTRALIA, POSTED IT AFTER MIDNIGHT HIS TIME ON THE NIGHT OF THE 9TH, THAT WOULD HAVE STILL BEEN BEFORE BITCOIN’S LAUNCH AT 3PM EST ON THE 9TH.) THAT POST WAS LATER REPLACED WITH THE RATHER CRYPTIC TEXT “BITCOIN – AKA BLOODY NOSEY YOU BE…IT DOES ALWAYS SURPRISE ME HOW AT TIMES THE BEST PLACE TO HIDE [IS] RIGHT IN THE OPEN.” SOMETIME AFTER OCTOBER OF THIS YEAR, IT WAS DELETED ENTIRELY.

May 8, 2009
The first post about Bitcoin on Hacker News: https://news.ycombinator.com/item?id=599852
"Well this is an exceptionally cute idea, but there is absolutely no way that anyone is going to have any faith in this currency."
jdoliner on May 9, 2009
Source:
@_unwriter (12 Nov 2018)
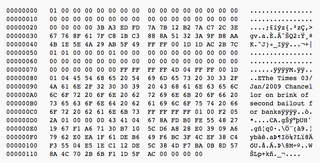
The Times 03/Jan/2009 Chancellor on brink of second bailout for banks
https://www.thetimes.co.uk/article/chancellor-a...

Jan 03 2009
https://blockexplorer.com
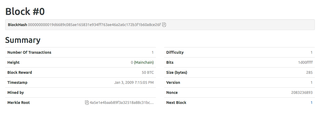
Genesis block
A genesis block is the first block of a block chain. Modern versions of Bitcoin number it as block 0, though very early versions counted it as block 1. The genesis block is almost always hardcoded into the software of the applications that utilize its block chain. It is a special case in that it does not reference a previous block, and for Bitcoin and almost all of its derivatives, it produces an unspendable subsidy.
Main network genesis block
Here is a representation of the genesis block as it appeared in a comment in an old version of Bitcoin. The first section defines exactly all of the variables necessary to recreate the block. The second section is the block in standard printblock format, which contains shortened versions of the data in the first section.
GetHash() = 0x000000000019d6689c085ae165831e934ff763ae46a2a6c172b3f1b60a8ce26f hashMerkleRoot = 0x4a5e1e4baab89f3a32518a88c31bc87f618f76673e2cc77ab2127b7afdeda33b txNew.vin[0].scriptSig = 486604799 4 0x736B6E616220726F662074756F6C69616220646E6F63657320666F206B6E697262206E6F20726F6C6C65636E61684320393030322F6E614A2F33302073656D695420656854 txNew.vout[0].nValue = 5000000000 txNew.vout[0].scriptPubKey = 0x5F1DF16B2B704C8A578D0BBAF74D385CDE12C11EE50455F3C438EF4C3FBCF649B6DE611FEAE06279A60939E028A8D65C10B73071A6F16719274855FEB0FD8A6704 OP_CHECKSIG block.nVersion = 1 block.nTime = 1231006505 block.nBits = 0x1d00ffff block.nNonce = 2083236893 CBlock(hash=000000000019d6, ver=1, hashPrevBlock=00000000000000, hashMerkleRoot=4a5e1e, nTime=1231006505, nBits=1d00ffff, nNonce=2083236893, vtx=1) CTransaction(hash=4a5e1e, ver=1, vin.size=1, vout.size=1, nLockTime=0) CTxIn(COutPoint(000000, -1), coinbase 04ffff001d0104455468652054696d65732030332f4a616e2f32303039204368616e63656c6c6f72206f6e206272696e6b206f66207365636f6e64206261696c6f757420666f722062616e6b73) CTxOut(nValue=50.00000000, scriptPubKey=0x5F1DF16B2B704C8A578D0B) vMerkleTree: 4a5e1e
Hash
The hash of the genesis block, 000000000019d6689c085ae165831e934ff763ae46a2a6c172b3f1b60a8ce26f, has two more leading hex zeroes than were required for an early block.
Coinbase
The coinbase parameter (seen above in hex) contains, along with the normal data, the following text:
"The Times 03/Jan/2009 Chancellor on brink of second bailout for banks"
This was probably intended as proof that the block was created on or after January 3, 2009, as well as a comment on the instability caused by fractional-reserve banking. Additionally, it suggests that Satoshi Nakamoto may have lived in the United Kingdom
Block reward
The first 50 BTC block reward went to address 1A1zP1eP5QGefi2DMPTfTL5SLmv7DivfNa though this reward can't be spent due to a quirk in the way that the genesis block is expressed in the code. It is not known if this was done intentionally or accidentally.[4][5][6] It is believed that other outputs sent to this address are spendable, but it is unknown if Satoshi Nakamoto has the private key for this particular address, if one existed at all.
from: https://en.bitcoin.it/wiki/Genesis_block

Jan 03, 2009
The bitcoin network came into existence with the release of the first open source bitcoin client and the issuance of the first bitcoins, with Satoshi Nakamoto mining the first block of bitcoins ever (known as the genesis block), which had a reward of 50 bitcoins. Embedded in the coinbase of this block was the text:
The Times 03/Jan/2009 Chancellor on brink of second bailout for banks
Block #0, BlockHash 000000000019d6689c085ae165831e934ff763ae46a2a6c172b3f1b60a8ce26f
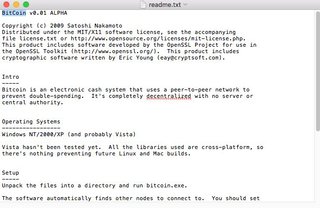
readme.txt
https://github.com/trottier/original-bitcoin/blob/master/readme.txt
BitCoin v0.1.3 ALPHA
Copyright (c) 2009 Satoshi Nakamoto
Distributed under the MIT/X11 software license, see the accompanying file license.txt or http://www.opensource.org/licenses/mit-license.php.
This product includes software developed by the OpenSSL Project for use in the OpenSSL Toolkit (http://www.openssl.org/). This product includes cryptographic software written by Eric Young (eay@cryptsoft.com).
Intro
-----
Bitcoin is an electronic cash system that uses a peer-to-peer network to prevent double-spending. It's completely decentralized with no server or central authority.
Operating Systems
-----------------
Windows NT/2000/XP (and probably Vista)
Vista hasn't been tested yet. All the libraries used are cross-platform, so there's nothing preventing future Linux and Mac builds.
Setup
-----
Unpack the files into a directory and run bitcoin.exe.
The software automatically finds other nodes to connect to. You should set your firewall to forward port 8333 to your computer so you can receive incoming connections, otherwise the nodes you can connect with will be limited.
To support the network by running a node, select:
Options->Generate Coins
and keep the program open or minimized. It runs at idle priority when no other programs are using the CPU. Your computer will be solving a very difficult
computational problem that is used to lock in blocks of transactions. The time to generate a block varies each time, but may take days or months, depending on the speed of your computer and the competition on the network. It's not a computation that has to start over from the beginning if you stop and restart it. A solution might be found at any given moment it's running. As a reward for supporting the network, you receive coins when you successfully generate a block.
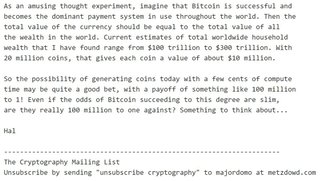
Bitcoin v0.1 released
Satoshi Nakamoto satoshi at vistomail.com
Fri Jan 16 11:03:14 EST 2009
> Dustin D. Trammell wrote:
> > Satoshi Nakamoto wrote:
> > You know, I think there were a lot more people interested in the 90's,
> > but after more than a decade of failed Trusted Third Party based systems
> > (Digicash, etc), they see it as a lost cause. I hope they can make the
> > distinction that this is the first time I know of that we're trying a
> > non-trust-based system.
>> Yea, that was the primary feature that caught my eye. The real trick
> will be to get people to actually value the BitCoins so that they become
> currency.
I would be surprised if 10 years from now we're not using
electronic currency in some way, now that we know a way to do it
that won't inevitably get dumbed down when the trusted third party
gets cold feet.
It could get started in a narrow niche like reward points,
donation tokens, currency for a game or micropayments for adult
sites. Initially it can be used in proof-of-work applications
for services that could almost be free but not quite.
It can already be used for pay-to-send e-mail. The send dialog is
resizeable and you can enter as long of a message as you like.
It's sent directly when it connects. The recipient doubleclicks
on the transaction to see the full message. If someone famous is
getting more e-mail than they can read, but would still like to
have a way for fans to contact them, they could set up Bitcoin and
give out the IP address on their website. "Send X bitcoins to my
priority hotline at this IP and I'll read the message personally."
Subscription sites that need some extra proof-of-work for their
free trial so it doesn't cannibalize subscriptions could charge
bitcoins for the trial.
It might make sense just to get some in case it catches on. If
enough people think the same way, that becomes a self fulfilling
prophecy. Once it gets bootstrapped, there are so many
applications if you could effortlessly pay a few cents to a
website as easily as dropping coins in a vending machine.
Satoshi Nakamoto
http://www.bitcoin.org
---------------------------------------------------------------------
The Cryptography Mailing List
Unsubscribe by send
Source:
metzdowd.com/pipermail/cryptography

DR CRAIG S WRIGHT GSE
No. 1: Geek ......... No. 2: Academic Junkie and highly over-qualified for everything (and still in Uni after 22 years...)
My Books
Over the years I have published a number of books. These are listed in reverse chronological order below and are linked for further detail. I list those books that are yet to be released first working towards the source and my first publication in the 90's.
Non-Fiction (Technical)
Official (ISC)2 Guide to the CISSP(R)-ISSMP(R) CBK
Set to be published 22nd May 2009.
I am the author of the "Law, Investigations, Forensics and Ethics" domain.
Cisco Router and Switch Forensics
Set to be published in early 2009, this book deals with the issues surrounding the forensic analysis of Cisco network devices. I am the author of the chapter on collecting volitile data from Cisco Routers.
Mobile Malware Attacks and Defense
I wrote the section covering the forensic analysis of MMC (Mobile Malware or Mobile Malicious Code). This is the best Book for Analyzing and Mitigating Mobile Malicious Code!
The IT Regulatory and Standards Compliance Handbook: How to Survive Information Systems Audit and Assessments (Paperback)
This is my first attempt at a sole publication. I authored the 750+ pages in this book as a technical guide to Information Technology Audit and Compliance. This publication covers Windows, Unix, Databases, the web, laws and planning and about anything else you can thin k of adding.
Check Point NGX R65 Security Administration
This title is a continuation of Syngress' best-selling references on Check Point's market leading Firewall and VPN products.
The Official CHFI Study Guide (Exam 312-49)
This is the first book I co-authored with Dave Kleiman. The other authors (which I am one) include: Jesse "James" Varsalone and Timothy Clinton.
This is the only official, EC-Council-endorsed CHFI (Computer Hacking Forensics Investigator) study guide. It was written for security professionals, systems administrators, IT consultants, legal professionals, IT managers, police and law enforcement personnel studying for the CHFI certification, and professionals needing the skills to identify an intruder's footprints and properly gather the necessary evidence.
Windows NT Security: Step by Step
The SANS Institute SANS Institute © 2001 (Co-Author)
This book is a little dated now with the depreciation of Windows NT but remains the definative guideline for NT security.
“A Comparative analysis of Firewalls” in “The Internet Hot Sheet”
Having been published in Sept 1999 and initially written in 1998, this book is long forgotten. Few people look for the quantitative history of Firewall products a decade ago. But you never know...
Planned
The following books are not yet published. These are on the proverbial drawing board and will be completed in the future.
Non-Fiction (Technical)
Finance, Economics and the Security Professional
This is a work in progress. The goal is to create a quantitative framework for modeling IT Security using economics, finance and stochastic control methods (including optimal control estimation). This is still a few years away.
The unified framework modeling book for CIP
This is an ongoing work lead by Bob Radvanovsky' of Infracritical. The expectation is for completion in 2009/2010.
Fiction
The Alia
This is my first attempt at writing fiction. I do not have a publisher as yet, but I am open to being contacted by one. I have a number of contacts in the technical writing field, but have not found one in the realm of science fiction as yet.
Source:
https://web.archive.org/web/2012...

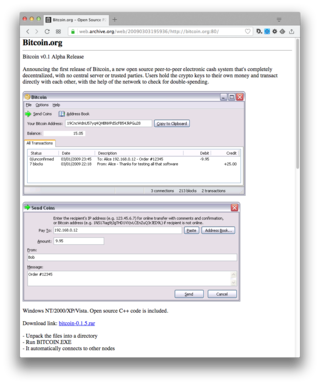
[bitcoin-list] Bitcoin v0.1 Alpha release notes
From: Satoshi Nakamoto <satoshi@vi...> - 2009-01-12 20:20:47
Release notes for Bitcoin v0.1 Alpha
Bitcoin is a new electronic cash system that uses a peer-to-peer
network to prevent double-spending. It's completely decentralized
with no server or central authority.
You can find screenshots and the download link at:
http://www.bitcoin.org
Windows only for now. Open source C++ code is included.
- Unpack the files into a directory
- Run BITCOIN.EXE
- It automatically connects to other nodes
If you can keep a node running that accepts incoming connections,
you'll really be helping the network a lot. Port 8333 on your
firewall needs to be open to receive incoming connections.
The software is still alpha and experimental. There's no guarantee
the system's state won't have to be restarted at some point if it
becomes necessary, although I've done everything I can to build in
extensibility and versioning.
You can get coins by getting someone to send you some, or turn on
Options->Generate Coins to run a node and generate blocks. I made
the proof-of-work difficulty ridiculously easy to start with, so
for a little while in the beginning a typical PC will be able to
generate coins in just a few hours. It'll get a lot harder when
competition makes the automatic adjustment drive up the difficulty.
Generated coins must wait 120 blocks to mature before they can be
spent.
There are two ways to send money. If the recipient is online, you
can enter their IP address and it will connect, get a new public
key and send the transaction with comments. If the recipient is
not online, it is possible to send to their Bitcoin address, which
is a hash of their public key that they give you. They'll receive
the transaction the next time they connect and get the block it's
in. This method has the disadvantage that no comment information
is sent, and a bit of privacy may be lost if the address is used
multiple times, but it is a useful alternative if both users can't
be online at the same time or the recipient can't receive incoming
connections.
Total circulation will be 21,000,000 coins. It'll be distributed
to network nodes when they make blocks, with the amount cut in half
every 4 years.
first 4 years: 10,500,000 coins
next 4 years: 5,250,000 coins
next 4 years: 2,625,000 coins
next 4 years: 1,312,500 coins
etc...
When that runs out, the system can support transaction fees if
needed. It's based on open market competition, and there will
probably always be nodes willing to process transactions for free.
Satoshi Nakamoto
_________________________________________________________________
Source:
https://sourceforge.net/p/bitcoin/mailman/message/21312004/


JavaScript is turned off.
Please enable JavaScript to view this site properly.