Oh my Satoshi
2014-12
Rumours continue to circulate as to the person who wrote the Bitcoin paper. Occasionally they are directed at self, but they can equally be directed at all the superlative financial cryptographers listed on this site and many others.
Let's take a moment to ask what we are doing here.
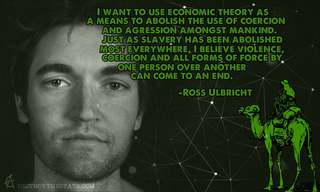
*Satoshi Nakamoto chose to do his work in anonymity*.
Or more technically in psuedoanonymity, as someone who claims to be 'anon' leaves no individual name and cannot be connected forward or backwards in time.
He, assuming it is a he, probably had good reasons for this. Which leaves us pondering why we would disrespect those reasons?
We, all of us, in today's Bitcoin world and yesterday's precursors to that world: cypherpunks, crypto, FC, privacy, mobile money, Tor, the Internet in general, ... we all hold privacy as an article of faith. We built the thing to protect people, and protect their privacy.
If Satoshi Nakamoto chose privacy, by what right or motive do we breach that? None.
There is no doctrine that permits anyone out there to arbitrarily strip out someone's privacy and remain one of us. Quite the opposite: our beliefs and existence call for protecting this person.
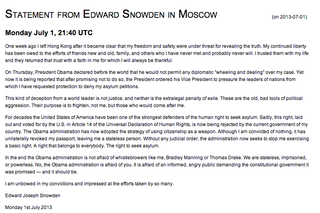
Indeed, revealing a stated secret of someone is more or less a crime in many contexts. Intelligence agencies can of course spy on whosoever, but they are not allowed to reveal that information (or, so says the doctrine). Police can demand information, but only pursuant to a crime -- probable cause and all that.
Freedom of the press? Public figures are by their nature afforded less 'privacy' because they are public; but they chose that path, and the courts grant the ability of the paparazzi only certain abilities, in line with the public figures' choice of public life. Paparazzi aren't allowed to chase ordinary folk, and Satoshi Nakamoto clearly chose to be out of that game.
Freedom of the press doesn't cut it. Nor does whistleblower status. Nor does 'public interest' as the public has no conceivable benefit to knowing more.
Those people who are digging around trying to strip this person's privacy are doing so because they haven't been called on it. Because they think it is cool. Because they feel intellectually challenged by the use of nyms, and using a nym is a licence to curiosity.
Wrong.
I call you now: what you are doing is wrong.
In some places it is a crime, because breaching privacy presumes there is another crime to follow: theft or fraud or extortion. It's a good presumption. In all civilised places, breaching privacy is an anathema. We all in this business -- save those sad damned souls with 5 eyes -- are working to *protect our community* not single out vulnerable persons and burn them at the stake.
Get you gone, get you out of our community. Anyone who publically reveals anyone else's private information has no common part with us. Anyone who goes on a witchhunt is our enemy. We are not doing all this work to give a few paparazzi a special scoop. To the person who eventually outs Satoshi Nakamoto I say this: the only place you'll be welcome is the NSA. Get ye there, scum.
In the words of that old film, we are all Satoshi Nakamoto.
Posted by iang at December 23, 2013 03:37 AM
http://financialcryptography.com/mt/archives/001463.html


The Hidden Dangers of Bitcoin
Published by Stefan Molyneux on 6 Nov 2014
Bitcoin is a revolutionary decentralized architecture which can be used for an untold number of incredibly valuable services – including the transfer of financial value. As Bitcoin adoption continues to expand, significant interests are threatened and early users could face an incredibly dangerous backlash. Please protect yourself, a fight is coming…
Source:
https://www.youtube.com/watch?v=tXBwcedQuQ0
1 mb blocksize limit keeps bitcoin free and decentralized
Published by Coin Tasker on 24.11.2014
The Bitcoin Song
Published by Tatiana Moroz on Jun 2, 2014
This is a live version of the Bitcoin Jingle that will become a full band version on the upcoming album. We have created the first ever artist crypto currency "Tatiana Coin" to fund that record and this song.
Source:
TatianaCoin.com
Vitalik Buterin explains Ethereum
3 minute explanation of Ethereum by inventor Vitalik Buterin.
Ethereum is a platform that makes it possible for any developer to write and distribute next-generation decentralized applications.
Borrowing the concept of distributed consensus and cryptographic proof that makes cryptocurrencies such as Bitcoin so effective in trustless payments, Ethereum extends the use of these technologies to trustless agreements. This allows developers to easily build innovative new products on a censorship and collusion-resistant foundation.
Ethereum will go live in Q4 2014, in the meantime we are regularly releasing alpha software so you can try your hand at building distributed applications.
Published by Ethereum on 29 Jul 2014
Source: ethereum.org




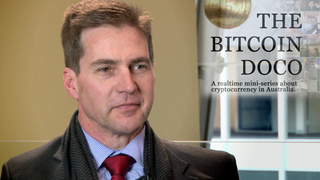
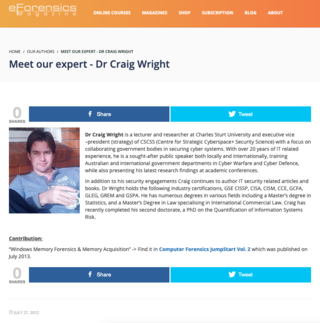
Interview with Craig Wright, Cyber Security Expert who trains governments on cyber defense
Published on 2 Jun 2014 by CGTN America
Satoshi Nakamoto - Thank you Bitcoin Community
published by aantonop
on Apr 22, 2014
Dorian Satoshi Nakamoto's message to the bitcoin community, at the conclusion of the Dorian Fundraiser.
Left: Dorian Satoshi Nakamoto
Right: Andreas M. Antonopoulos


Vitalik Buterin reveals Ethereum at Bitcoin Miami 2014
Vitalik Buterin, Founder and Inventor, introduces Ethereum at the Bitcoin Miami conference 2014. Vitalik received a standing ovation for the project which stands to change how the world relates to currency and financial instruments.
Published by Ethereum on 1 Feb 2014
The Godfather of Ethereum: Yanislav Georgiev Malahov
Posted by Yanislav Georgiev Malahov on May 25, 2015
Often people asked me in the past: “What do you do with/for Ethereum?”. I always had a hard time answering this. The reason is, that I was kind of involved in Ethereum even before there was a name for it. So let me try to explain my connection to Ethereum a bit…
About a year and a half ago in autumn 2013, I was working as the lead developer with Vitalik Buterin (who later became the initiator of the Ethereum project) on another project with the name ‘Keidom’ (now called ascribe.io). The idea behind Keidom/Ascribe was to develop a custom colored-coin web-wallet for registering and transfering digital art in a secure way, based on the Bitcoin blockchain, with build-in proof-of-existence. We developed a working prototype during September and November 2013.
A little background
I met Vitalik for the first time in Berlin for the Berlin Bitcoin Summer Meetup and traveled with him and Mihai Alisie to Barcelona, to the (in)famous Calafou camp with an anarchistic touch. I met Vitalik again in Milan together with Amir Taki and then later in Vienna, together with the Mycelium guys.
Vitalik and me standing on the top of Montserrat near Calafou, near Barcelona.
During our Vienna meeting we set the goal to work together on the Keidom/Ascribe colored-coin wallet. From the beginning on, we were working in a distributed fashion. Vitalik left for Zurich and I went back to Berlin. About two weeks later there was the Amsterdam Bitcoin conference where we met again. Then Vitalik left Europe afterwards for Israel to start working on the side for the Mastercoin project and I went back to Berlin for a short time before leaving for Bulgaria for all of November.
Vitalik, who is considered ‘the father of Turing-complete financial scripts’ by the founder of Mastercoin ‘JR’, and me stayed in touch almost every day because of our colored coins wallet, so that one evening in the mid of November I asked Vitalik more about what Mastercoin actually is. I never really spend time to understand it because of the poor quality of the whitepaper, the unfortunate name “Mastercoin” (got recently rebranded to Omni), and the not-quite-right name ‘The Second Bitcoin Whitepaper’, as if Satoshi Nakamoto wrote it himself. Out of this conversation late at night Ethereum might have been born, as far as I can tell. To verify this I attach the chat log so that everyone can judge himself.
A few weeks later I read about Ethereum on reddit. I immediately knew what it was about…
In the manner of JR, I shall call myself from now on: “Godfather of Ethereum”. This is a joke, of course. Or maybe, not ;)
“Holy Grail of Decentralized Computing”
Back then we wanted to build something like Ethereum on top of Primecoin because it seemed like the most advanced and innovative crypto-currency at this time. Especially the innovation in the Proof-of-Work was significant. For the first time the work had more meaning than just securing the network and distributing coins.
In summer 2013, I had verbalized the “Holy Grail of Decentralized Computing”, inspired by Primecoin’s Proof-of-Work. I.e., to find computational problems which are hard-to-solve and which have at the same time meaningful solutions which are easy-to-prove, so that one can create a a blockchain-based crypto-currency and reward coins for solving the problems. I never really developed the idea though.
I observed the development of Vitalik’s Ethereum project for a while, took part at the first Meetup in Miami at the North American Bitcoin Conference in January 2014 but ultimately decided not to get more deeply involved because of personal reasons. Later on I spend quite some time with Ethereums CTO, Gavin Wood, in San Francisco and Berlin, where we developed an idea to solve the scalability issues of blockchain technology. I never had a job at Ethereum or received any form of compensation. Just some stories to share, and this is what I do here.
First Ethereum Meetup in Miami in January 2014 — I am the second from left in the back row.
Source:
medium.com/@yanislav

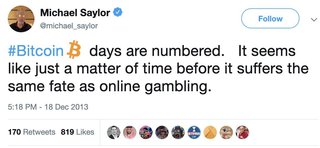
Why Bitcoin Must Die. Long Live Bitcoin 2.0.
published by Bill Frezza, Feb 7, 2014
One day, there will be a global digital currency in widespread commercial use whose value will not be controlled by central banks. Governments can forestall this day, as they have for the past 20 years since the first digital currencies were launched, but the market demand for an alternative to inflation-prone fiat money that can be conveniently, securely, and inexpensively exchanged over digital networks will be too strong to resist. Alas, the currency described above will not be Bitcoin, at least not in its current configuration.
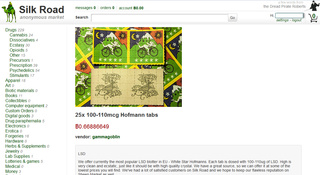
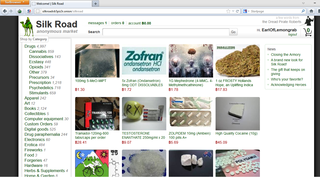
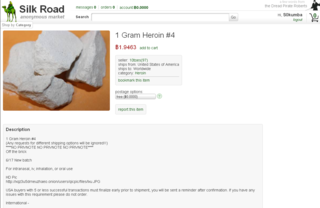
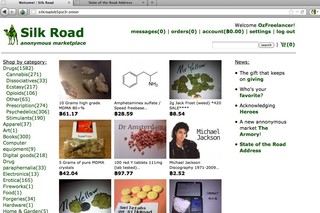
Why not today’s Bitcoin? Because the digital currency of the future must choose between two mutually exclusive paths. It can either be anonymous, enabling black market transactions in the shadow economy, or it can be fully compliant with the growing body of know your customer, anti-money laundering laws that constrain global financial markets. A single digital currency cannot do both.
Read on
Source:
https://www.forbes.com/sites/billfrezza/2014/



Keynote: Mike Hearn, Bitcoin Core Developer
Mike Hearnshows a critical view of the development process behind bitcoin. Only 10 people make the bitcoin software core. This is done in a non sustainable way and needs to change.
Published by Dutch Blockchain Conference on 24 May 2014




Aussie Technologists Plan To Open The World’s First Bitcoin-Based Bank This Year
Posted by Liz Tay Feb. 12, 2014, 4:00 PM
Sydney technology firm Hotwire PE is months away from opening the world’s first Bitcoin-based bank after a year of talks with regulators in the UK, US, Australia and Singapore.
CEO Craig Steven Wright said Denariuz Bank would begin accepting deposits in the second half of 2014 and would eventually offer Bitcoin-based equivalents of conventional savings accounts, term deposits, credit and debit cards, and loans.
One Bitcoin currently buys about $US667 or $A736. Wright said Denariuz would launch with a global pool of more than 100,000 Bitcoin ($A73.6 million) from its backers.
Eventually, the bank hopes to have a million customers globally.
Denariuz will have no physical branches, nor does Wright expect customers to rely on Bitcoin ATMs.
Instead, the company has built an online “eWallet” that, like today’s online banking applications, will let customers access their accounts on their desktop and mobile devices.
Wright, who has worked in information security for 15 years and is a lecturer at the Charles Sturt University, also hopes to strike an agreement with a payments card provider like Visa, American Express or Cuscal to facilitate day-to-day Bitcoin transactions.
A growing number of Australian merchants have begun accepting Bitcoin, but Denariuz will provide currency exchange through its “Coin-Exch” platform when needed, he said.
Wrestling with regulators and politics
Hotwire PE has about 50 staff in Australia and the US, of which about 45 are based down under.
Wright said regulatory discussions had been particularly difficult in Australia, where the ATO has yet to clarify how it will handle Bitcoin-related GST.
But he was committed to opening Denariuz Bank in Australia because “I’m Australian and I’m still here”.
Wright hopes to finalise talks with the tax office in the coming weeks, and with company and banking regulators ASIC and APRA within the year.
The latter has yet to decide on whether Denariuz is eligible for a full banking licence, without which it will “be hanging off a third-party Australian Financial Services Licence” (AFSL), Wright explained.
PayPal also operates on a restricted banking licence in Australia.
APRA’s decision relies on whether it deems Bitcoin a “financial instrument” or money – a definition that international regulators have also grappled with.
Bitcoin is not considered “money” or “currency” under Singapore’s GST act, the country’s Inland Revenue Authority stated last month.
“[Authorities] have to understand that Bitcoin is money, and should be treated as such,” Wright said. “Unfortunately, there’s a lot more political lobbying involved than I would have liked.”
Hotwire PE this week described Denariuz as an effort to “bring about the legitimisation of Bitcoin in Australia and throughout the world”.
In the interim, Wright said the company would adhere to all existing laws and regulations including Basel III and its backers would wear the risk of exchange rate fluctuations.
He expected a stock market listing to be in the pipeline but declined to discuss details.
Source:businessinsider.com.au
Bitcoin bank seeks regulatory approval
Posted by James Mitchell on 12 February 2014
Despite increasing talk of a bubble in the peer-to-peer Bitcoin economy, an Australian company is looking to ‘legitimise’ the online currency with the proposed launch of a Bitcoin bank.
Web technology company HotwirePE yesterday announced the launch of Denariuz Bank, which it claimed would be “the first bank based solely on crypto-currency in the world”.
Speaking to InvestorDaily, HotwirePE chief executive Dr Steven Wright said his firm was working with the Australian Taxation Office and ASIC and is aiming to “have a full banking licence from APRA based on Bitcoin”.
HotwirePE has been working closely with senior government officials for the last 10 months to help them understand Bitcoin and how to regulate it – and the ATO is currently considering the tax treatment of Bitcoin, according to a HotwirePE statement.
“We seek to turn Bitcoin into an internationally-regulated currency and investment tool that uses secured micro-payments for e-commerce transactions between anyone, at anytime, anywhere, and on any-device,” said Dr Wright.
“The great thing with Bitcoin is you can’t loan more than you have; you can have a variety of different contracts and derivatives and all the rest actually set up, but you are limited in that you can’t loan Bitcoins that you don’t actually have,” he said.
With multi-layer security in place, Denariuz will guarantee the safety and protection of customer’s Bitcoins in its secured cold storage vault, removing internet risks and security concerns, according to HotwirePE.
“The UK recently reversed its classification of Bitcoin and said VAT would not be due on sales using Bitcoins,” said Dr Wright said.
“We hope the ATO follows suit and does not force GST to be applied to transactions using the crypto-currency.
“It would be an embarrassment if the regulatory outcome excludes Australia … Incorrect handling of what is essentially money could see a $100 million investment forced to move away from Australia,” said Dr Wright.
However, the virtual currency debate is a continuing one and Bitcoin is not without its detractors.
Euro Pacific Capital chief executive Peter Schiff told CNBC, “the online currency more closely resembles tulip mania 2.0”.
"A bubble is a bubble," he said, "and there's a bubble in Bitcoins."
Yesterday, the Wall Street Journal reported on a ‘technical glitch’ that had impacted the currency.
“A leading Bitcoin exchange Monday blamed a long-unresolved technical issue for its decision to abruptly halt customer withdrawals last week,” the Wall Street Journal reported.
“Prices of Bitcoin were sent reeling to their lowest level in two months Monday — quickly falling to below $550 from Friday's close of $703.57, according to an index compiled by CoinDesk, a Bitcoin-data provider based in London,” the paper said.
“The exchange, Tokyo-based Mt. Gox, said the software issue could affect all Bitcoin transactions to third parties and needed to be addressed in cooperation with the core development team of the payment system,” it said.
HotwirePE’s Dr Wright said the Japanese system glitch is “unfortunate to say the least”.
“There is a reason we have taken a lot longer to come to market the way we have; we want everything to be rock solid first,” he said.
“That has meant rewriting the Bitcoin daemon [programming code] and a whole lot of other things that we’ve had to do.”
Dr Wright said that these glitches do lead to a lot of volatility in the market.
“That is why we are working with the tax office and ASIC and thinking down the track to have a full banking licence from APRA based on Bitcoin,” he said.
Dr Wright confirmed he is meeting with ATO officials in Canberra this week.
Source: investordaily.com.au


Published by Alex Biles on May 08, 2013
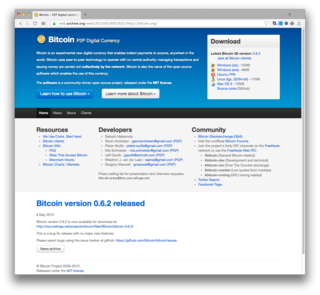
It's likely that you've heard about bitcoin and its legendary rise by now.
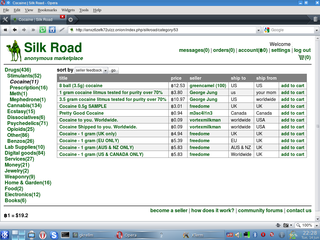
A pseudonymous Japanese hacker laid out the blueprint for the peer-to-peer digital currency shortly before vanishing into thin air.
Primarily the province of Internet hackers, web savvy drug launderers and libertarian techies, bitcoin went mainstream in 2013. After an intense March and early April, the currency saw a unit of the virtual money climb from $15 USD to an astounding $200 on April 9.
Of course, this peak was accompanied by a sharp correction, which saw bitcoin lose about half its value. The digital dough has held its ground as a vehicle for speculation, and more importantly as a hedge against financial instability, particularly among the eurozone's more decimated economies. This is in the wake of mass scrutiny following the crash, which the currency's detractors deemed its end.
As of this writing, bitcoins are trading at $113.
Read on
Source: benzinga.com
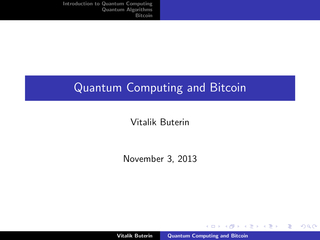
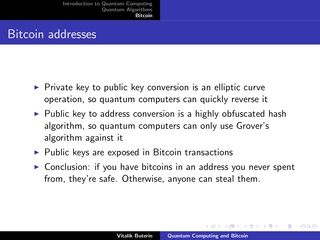
Quantum Computing and Bitcoin
Vitalik Buterin explains what quantum computers are, what they can and cannot do, and the implications they may have to the future of Bitcoin. The lecture took place on November 3rd 2013.
Published by Bitcoin Israel on 5 Nov 2013
Bitcoin May Be the Global Economy's Last Safe Haven
The anarchist virtual currency may be a hoax. It could also be the global economy’s last safe haven
by Paul Ford, March 28, 2013
"The Internet is a big fan of the worst-possible-thing. Many people thought Twitter was the worst possible way for people to communicate, little more than discourse abbreviated into tiny little chunks; Facebook was a horrible way to experience human relationships, commodifying them into a list of friends whom one pokes. The Arab Spring changed the story somewhat. (BuzzFeed is another example - let them eat cat pictures.) One recipe for Internet success seems to be this: Start at the bottom, at the most awful, ridiculous, essential idea, and own it. Promote it breathlessly, until you’re acquired or you take over the world. Bitcoin is playing out in a similar way. It asks its users to forget about central banking in the same way Steve Jobs asked iPhone users to forget about the mouse."
Source:
https://www.bloomberg.com/news/articles/2013-03...
Wang's B machines are efficiently universal, as is Hasenjaeger's small universal electromechanical toy
Turlough Neary, Damien Woods, Niall Murphy, Rainer Glaschick
Submitted on 30 Mar 2013
In the 1960's Gisbert Hasenjaeger built Turing Machines from electromechanical relays and uniselectors. Recently, Glaschick reverse engineered the program of one of these machines and found that it is a universal Turing machine. In fact, its program uses only four states and two symbols, making it a very small universal Turing machine. (The machine has three tapes and a number of other features that are important to keep in mind when comparing it to other small universal machines.) Hasenjaeger's machine simulates Hao Wang's B machines, which were proved universal by Wang. Unfortunately, Wang's original simulation algorithm suffers from an exponential slowdown when simulating Turing machines. Hence, via this simulation, Hasenjaeger's machine also has an exponential slowdown when simulating Turing machines. In this work, we give a new efficient simulation algorithm for Wang's B machines by showing that they simulate Turing machines with only a polynomial slowdown. As a second result, we find that Hasenjaeger's machine also efficiently simulates Turing machines in polynomial time. Thus, Hasenjaeger's machine is both small and fast. In another application of our result, we show that Hooper's small universal Turing machine simulates Turing machines in polynomial time, an exponential improvement.
Source: arxiv.org

Why the blocksize limit keeps Bitcoin free and decentralized
Published by Keep Bitcoin Free! on 16 May 2013
The blocksize limit is what ensures everyone can participate in the Bitcoin network, and it ensures everyone can participate anonymously should they choose too. Some people want to remove this protection to make Bitcoin scale, but we can have the best of both worlds: high transaction volume and true decentralization with off-chain transactions. Learn more at http://keepbitcoinfree.org
Source:
https://www.youtube.com/watch?v=cZp7UGgBR0I


Hotwire PE Group
Founded in 2013
Mission
Our mission is to lead the development of technologies that will reinvent the internet, one transaction at a time
About
Hotwire PE is creating systems that merge the benefits of traditional banking and finance with payment technologies of the future.
@hotwirepegroup
press@hotwirepe.com
http://www.hotwirepe.com
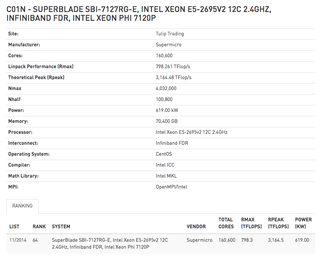
Craig Steven Wright
Chief Executive Officer
DeMorgan Limited
September 2014 – Present (1 year 4 months)
DeMorgan is a pre-IPO Australian listed company focused on alternative currency, next generation banking and reputational and educational products with a focus on security and creating a simple user experience.
We control the following companies:
• Panopticrypt Pty Ltd
• Cloudcroft Pty Ltd
• Coin-Exch Pty Ltd
• C01N Pty Ltd
• CHAOS AND NONLINEAR FORECASTABILITY IN ECONOMICS AND FINANCE PTY. LTD.
• DASO Pty Ltd
• Denariuz Pty Ltd
• Denariuz Pte Ltd (Singapore)
• EzAs Pty Ltd
• Integyrz Pty Ltd
• DeMorgan Ltd (Panama)
• Pholus Pty Ltd
• Zuhl Pty Ltd
• Zuhl Corp Ltd (USA)
• Misfit Games Pty Ltd
• Denariuz Ltd (UK)
Our group of companies has received a series of Advance Findings from AusIndustry around the two HPC systems we run and the AI and machine learning activities we conduct. In total, we have received Core Technology and Advance Finding certificates for 110 million in research activities.
In the six years since the first company in the group started, we have completed several Bitcoin based research projects that have lasted over and are now ready to start commercialising.
“Craig is a little bit crazy, as in Orville & Wilbur Wright craziness of deciding to add an engine to a glider. … a true visionary”.
Steven Lipke, employee at Hotwire PE

Bitcoin And The World At Large
Vitalik Buterin is the lead writer and co-founder of Bitcoin Magazine, and has been actively involved in Bitcoin-related projects. His interests include math, computer science, online education, economics and linguistics.
Published by BoxxyBrassin on 31 Aug 2013
Published by Satoshi Pollen on 21 Aug 2013


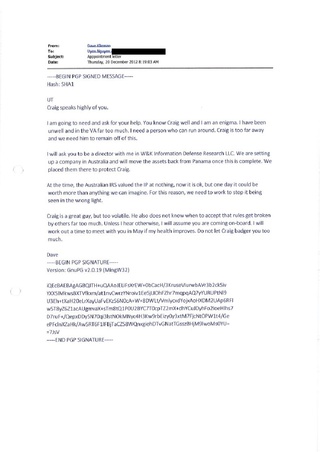
Dave Kleiman - RIP (1967 - 2013)
Published by Craig Wright on Apr 29, 2013
Source:
https://web.archive.org/web/20130509011754/

I Think I Know Who Satoshi Is
The creator of Bitcoin-- who I think he is, and why.
Published by TheTedNelson on 17 May 2013

Bitcoin Explained
Published by Duncan Elms on 9 Apr 2013
A short video looking at 'Bitcoin', a decentralized digital currency. This is a self funded personal project,
If you would like to make a Bitcoin donation for the video, please do so to 1P9wrpA2UQ2GEmMpt81Ch3Wt4poq5LhpiW
Directed, Designed and Animated by Duncan Elms - duncanelms.com
Written and Voiced by Marc Fennell - marcfennell.com
This project was done between other jobs. Therefore some of the stats are not up to date. For more info please see en.wikipedia.org/wiki/Bitcoin
Satoshi Nakamoto is (probably) Nick Szabo
Published by Dec 1, 2013 by LikeInAMirror
https://likeinamirror.wordpress.com/2013/12/01/satoshi-nakamoto-is-probably-nick-szabo/
Daniel Larimer - CEO, Invictus Innovations Introduces BitShares
Published on Oct 20, 2013

Craig Steven Wright
Chief Executive Officer
Hotwire Pre-Emptive Intelligence Group
The world grows through change and knowledge. To thrive, people need to develop wisdom in a social web. To enable this, we must look ahead, understand the trends and forces that will shape society and business in the future and move swiftly to prepare people for what's to come. We will help the world to get ready for tomorrow today. That's what our 2020 Vision is all about. It creates a long-term destination for our business and provides us with a "Roadmap" for winning together with our community and the society we will help to foster through trust and assurance.
Our Mission
Our Roadmap starts with our mission, which is enduring. It declares our purpose as a company and serves as the standard against which we weigh our actions and decisions.
• To make the world wiser and better...
• To inspire enduring optimism and trust...
• To create value and make a difference.
Hotwiring the world
The world grows through change and knowledge. To thrive, people need to develop wisdom in a social web. To enable this, Hotwire PE must look ahead, understand the trends and forces that will shape society and business in the future and move swiftly to prepare people for what's to come. We will help the world to get ready for tomorrow today. That's what our 2020 Vision is all about. It creates a long-term destination for our business and provides us with a "Roadmap" for winning together with our community and the society we will help to foster through trust and assurance.

The Church of Bitcoin was founded on October 25th 2012 in order to grant Bitcoin users a non regional spiritual outlet and to escape oppression by existing religious groups. Its homepage may be at bitprayer.com
The Church of Bitcoin is guided by eleven commandments:
- Praise Satoshi.
- Honor the blockchain.
- Thou shalt not fork thine own family.
- Keep the network holy.
- Thou should not covet another man's wallet.
- Do unto others as you would have them DDoS you.
- Thou shalt not swear unto another man that thine payment hath not been received until all of the blockchain hath been downloadeth.
- Salt thine passwords.
- Hack thine planet.
- Keep thine woman, Bruces and Atlases in separate camps if they are unclean.
- Troll harder.
See also: https://en.bitcoin.it/wiki/Church_of_Bitcoin
CRAIG STEVEN WRIGHT
SENIOR MANAGEMENT EXECUTIVE INFORMATION SECURITY SPECIALIST
► CTO / CIO / CISO /CSO
Multi-certified Expert in Enterprise Security and Cloud Strategies
If you want to sell me SEO, look at what I do first.
http://www.top500.org/site/50547
Respected executive and technology leader delivering proven ability to capitalize on enterprise-level technologies and pioneering strategies. A sought-after internationally recognized author and public speaker, delivering solutions to government and corporate departments in SCADA security, Cyber Security and Cyber Defense, as well as leading the uptake of IPv6 and Cloud technologies. Drives innovative strategies that result in the strategic redevelopment and invigoration of both startups and established firms. Futurist, thought leader and expert with proven innovation in program leadership, execution design and strategic redevelopment.
► Technology Leadership Results
Trusted member of senior executive team driving results driven innovation focused strategies that take core business competencies and deliver profitable client centric results and growth.
► Centre of Excellence Leader delivering to government and corporate clients pathways to IPv6 and secure cloud based solutions.
► Led the migration of a new core banking platform based on .Net and cloud technologies delivering a forward client centered banking platform.
► Oversight and governance in the profitable management of a $5 billion financial trust.
Distinguished by designing the security architecture and environment for Lasseter’s On-Line Casino allowing approval by the NT Government for the first online gaming license globally.
Developed board level security policies and procedural practices within Mahindra and Mahindra, India’s largest vehicle manufacturer. The Mahindra group employee over 50,000 people in total and has numerous business interests from Car to Tractor manufacture, through to IT outsourcing.


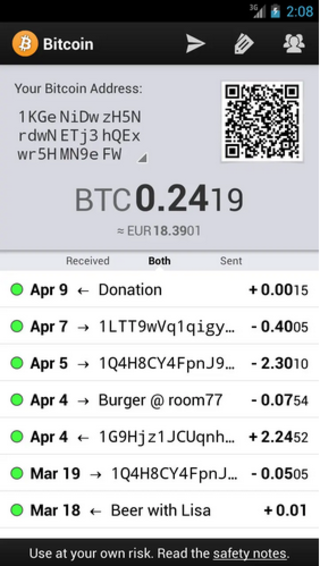
Berlin BITCOIN meetup @ Room 77
Published by EmilyChesher on 10 Oct 2012
The Global Intelligence Files
The Bitcoin currency
On Monday February 27th, 2012, WikiLeaks began publishing The Global Intelligence Files, over five million e-mails from the Texas headquartered "global intelligence" company Stratfor. The e-mails date between July 2004 and late December 2011. They reveal the inner workings of a company that fronts as an intelligence publisher, but provides confidential intelligence services to large corporations, such as Bhopal's Dow Chemical Co., Lockheed Martin, Northrop Grumman, Raytheon and government agencies, including the US Department of Homeland Security, the US Marines and the US Defence Intelligence Agency. The emails show Stratfor's web of informers, pay-off structure, payment laundering techniques and psychological methods.
https://wikileaks.org/gifiles/docs/28/2880713_re-ct-discussion-the-bitcoin-currency-.html
Bernhard von Nothaus, Monetary Architect of the Liberty Dollar
Rare Interview with Visionary Bernhard von Nothaus. The Monetary Architect of the Liberty Dollar was charged and found guilty of federal crimes for "making, possessing, and selling his own currency"



The Byzantine Generals' Problem
A number of Byzantine Generals each have a computer and want to attack the King's wi-fi by brute forcing the password, which they've learned is a certain number of characters in length. Once they stimulate the network to generate a packet, they must crack the password within a limited time to break in and erase the logs, lest they be discovered. They only have enough CPU power to crack it fast enough if a majority of them attack at the same time.
They don't particularly care when the attack will be, just that they agree. It has been decided that anyone who feels like it will announce an attack time, which we'll call the "plan", and whatever plan is heard first will be the official plan. The problem is that the network is not instantaneous, and if two generals announce different plans at close to the same time, some may hear one first and others hear the other first.
They use a proof-of-work chain to solve the problem. Once each general receives whatever plan he hears first, he sets his computer to solve a difficult hash-based proof-of-work problem that includes the plan in its hash. The proof-of-work is difficult enough that with all of them working at once, it's expected to take 10 minutes before one of them finds a solution and broadcasts it to the network. Once received, everyone adjusts the hash in their proof-of-work computation to include the first solution, so that when they find the next proof-of-work, it chains after the first one. If anyone was working on a different plan, they switch to this one, because its proof-of-work chain is now longer.
After about two hours, the plan should be hashed by a chain of 12 proofs-of-work. Every general, just by verifying the difficulty of the proof-of-work chain, can estimate how much parallel CPU power per hour was expended on it and see that it must have required the majority of the computers to produce in the allotted time. At the least, most of them had to have seen the plan, since the proof-of-work is proof that they worked on it. If the CPU power exhibited by the proof-of-work is sufficient to crack the password, they can safely attack at the agreed time.
Source:
https://bitcointalk.org/oldSiteFiles/byzantine.html
Original from bitcoin.org

The first Bitcoin reference in television history aired on The Good Wife in 2012, when it was only worth $3.41
Source: reddit.com

JavaScript is turned off.
Please enable JavaScript to view this site properly.